Government employees must comply with policies on information security regulations, online security practices, social networking usage, internet addiction, online cyberthreats and other related habits. These activities are considered cybersecurity behaviors. Government social media (GSM) accounts are increasingly used to educate employees about cybersecurity risks. To support the effectiveness of cybersecurity practices in government organizations, the purpose of this study is to investigate the impacts of GSM and organizational policy compliance on employees’ cybersecurity awareness, motivation and behaviors.
Data were obtained by administering a questionnaire survey to public personnel in Vietnam. A total of 330 valid responses were obtained, and the research hypotheses were tested using partial least squares–structural equation modeling.
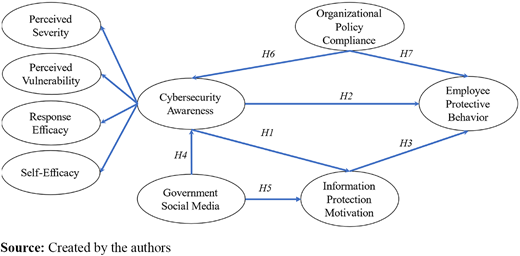
First, cybersecurity awareness enhances information protection motivation and employee protective behavior. Second, GSM has positive impacts on cybersecurity knowledge and information protection motivation. Third, there is a strong positive association between information protection motivation and employee protective behavior. Finally, while organizational compliance significantly increases cybersecurity awareness, its impact on employee protective behavior is ind irect.
This research enhances the literature on the behavioral dimension of cybersecurity. The primary objective of this study is to assess the influence of cybersecurity awareness on protective behaviors rather than intents and attitudes alone. Furthermore, this research integrates protection motivation theory and cultivation theory to provide a more thorough assessment of cybersecurity awareness and protective behavior. By investigating the impact of GSM on the level of cybersecurity awareness among employees within government organizations, this study provides valuable insights into the efficacy of recent governmental initiatives aimed at fostering cybersecurity.
1. Introduction
Information and communication technologies (ICT) have become deeply integrated within national infrastructures and nearly all aspects of daily life (Li et al., 2022). The unprecedented penetration of ICT has helped organizations gain competitive advantages through improvements in system accessibility, communication speed and efficiency and reduced operating costs (Hasan et al., 2021). The adoption of digital finance has been more influenced by its potential benefits than by its perceived risks (Jain and Raman, 2023). Nonetheless, digital advancements can pose serious cybersecurity threats to organizations because of their dynamic features, complex multifunctionality and interconnectedness (Fosch-Villaronga and Mahler, 2021; Li et al., 2019). Cyberattacks on businesses of all sizes and industries are increasing in frequency, volume and sophistication (Lu and Xu, 2019). Cyberattacks can cause severe damage to organizations by intentionally or unintentionally exposing confidential information (Ou et al., 2022). However, there are significant gaps in our understanding of the variations in cybersecurity awareness, knowledge and behavior among employees.
The best way to reduce the threat of cyberattacks is to increase individual awareness. The term “cybersecurity awareness” refers to the extent to which individuals understand the significance of information security and their obligations to implement adequate levels of information security control to safeguard an organization's data and networks (Shaw et al., 2009). Most individuals do not fully understand which instruments are required for protection against cyber risks (Zwilling et al., 2022). In addition, as the world becomes increasingly digitally interconnected, the most effective strategy for enhancing cybersecurity awareness is to improve the know-how of both citizens and employees in the business and public administration sectors (Zwilling et al., 2022). To do so, organizations must establish policy compliance. Organizational policy compliance refers to the extent to which individuals conform to the prescribed rules, regulations, standards and guidelines of an organization. Organizational policies generally encompass a broad spectrum of domains, including but not limited to code of conduct, information security, data privacy, safety standards and human resources practices. Adherence to organizational policies guarantees uniformity, equity and legality in the activities and conduct of employees or members of the organization (AlKalbani et al., 2017; Bauer et al., 2017). However, empirical studies of the relationships between organizational policy compliance with cybersecurity awareness and employee protective behavior have yielded conflicting findings (Lee et al., 2004; Lee and Larsen, 2009; Li et al., 2019). Investigating these relationships in the public sector of an emerging market, such as Vietnam, has the potential to add new insights.
Moreover, the role of protection motivation is significant in influencing employee behaviors pertaining to compliance with information security policies. Particularly, information protection motivation is the degree of employees’ motivation to implement preventive measures against cyberattacks (Ma, 2022; Posey et al., 2015; Vrhovec and Mihelič, 2021). This motivation is the result of threat appraisal and coping appraisal processes and operates as an intervening variable similar to other motives that induce, sustain and direct employees’ activities (Martens et al., 2019). According to the protection motivation theory (PMT), employees will take measures to protect themselves against cybersecurity risks when they see a threat and believe they possess the necessary abilities to handle the potential danger. However, individuals frequently have an insufficient awareness or understanding of how to safeguard themselves against cyberattacks (Klein and Zwilling, 2023). Employee protective behaviors are the steps that employees take to correctly address cybersecurity concerns (Li et al., 2019; Tang et al., 2021).
An organization’s information security system is affected by many factors at the individual and organizational levels. Behavioral factors have recently been the focus of attention because employees directly control the accessibility, confidentiality and integrity of information (Ma, 2022). More than 70% of security breaches are because of employee negligence or inadequate compliance with organizational cybersecurity protocols (Alshaikh et al., 2021). In some cases, employees are not sufficiently aware of the variety of attacks that are constantly altering the corporate security landscape (Zwilling et al., 2022). For example, opening an email with an unfamiliar file extension or providing illegal access to others has the potential to expose the entire organization to cybersecurity breaches. In addition, employees tend to overlook mandatory security measures when completing tasks (Ifinedo, 2012), especially when managing multiple tasks simultaneously and facing stringent deadlines (Chowdhury et al., 2019). Thus, given the important role of employees in cybersecurity, the government and organizations should examine and prioritize practices that effectively enhance employees’ awareness and protective behaviors.
Social media encompasses apps and social network platforms that are part of Web 2.0 technology. These platforms enable the development, diffusion and transmission of knowledge across communities of users (Del Vecchio et al., 2020). The growing popularity of social media influencers has led to the widespread adoption of influencer marketing in business strategies (Vrontis et al., 2021). Government social media (GSM) accounts enhance the dissemination of official information and provide new platforms that are accessible and beneficial to the general public (Islm et al., 2021). Specifically, GSM is the online presence established and overseen by a governmental department or organization across various social media platforms (Tang et al., 2021). Governments can use GSM to quickly provide information to citizens, keep them aware of the status of threats, prevent the spread of false data and provide assistance to victims of disasters (Guo et al., 2021).
Specifically, studies of GSM have primarily focused on citizens' reasons for interacting with GSM and categorizing emergency messaging strategies (Tang et al., 2021). The impact of GSM on citizens during acute outbreaks of disease, such as COVID-19 or measles, has also been explored. However, there is a notable gap in understanding the impact of GSM on persistent issues spanning decades, such as cybersecurity attacks. A comprehensive understanding of these effects from a behavioral perspective will help GSM operators formulate effective engagement strategies and craft valuable messages. Likewise, governments can use social media accounts to increase awareness of cybersecurity threats, but the effectiveness of these efforts has not been established. Importantly, limited research has been conducted on the expansion of cultivation theory within the framework of GSM.
To address the above gaps, this study integrates PMT and cultivation theory to examine the effects of individual factors (awareness and motivation), organizational factors (cybersecurity policy) and GSM on employees’ protective behaviors related to cybersecurity. The following research questions are addressed:
How do organizational policies affect employees’ cybersecurity awareness and behaviors?
How does government social media influence employees’ cybersecurity awareness and protective behaviors?
How does employees’ cybersecurity awareness affect their protective behaviors?
The broad expansion of internet accessibility has significantly increased the complexity and frequency of cyberattacks, with extensive adverse consequences in multiple sectors, including businesses, industries and political administrations. In the face of these growing dangers, governments around the world have taken specific actions to strengthen the security of networks, especially those that are crucial for national defense. In Vietnam, cyberattacks mainly target key information infrastructures of central authorities and large financial corporations. Enhancing the legal structure that regulates network information security can help safeguard critical national defense information. A crucial component of this undertaking is evaluating the capacity and operational knowledge of network overseers, as efficiently protecting against cyberattacks requires proficient staff. Furthermore, the proper management of network information security depends on a comprehensive regulatory framework to reduce risks and effectively address cyberthreats. The Cybersecurity Law of Vietnam, which was implemented on January 1, 2019, highlights the government's dedication to maintaining societal order and safety in cyberspace. This legislation clearly outlines the duties and obligations of pertinent authorities, companies and individuals. However, additional studies of guidelines and organizational policy compliance are needed to guarantee the safety and security of employees as they navigate the digital realm, specifically in relation to internet usage and online transactions. In Vietnam, social media platforms are widely used by government organizations and officials, and the predominant platforms for GSM are Facebook, Zalo, Viber, YouTube, TikTok and Instagram.
This study contributes significantly to the literature on cybersecurity in Vietnam, especially behavioral aspects, by measuring the effects of cybersecurity awareness on actual protective behaviors rather than merely behavioral intentions, attitudes and likelihood. In addition, by integrating four components of the PMT and cultivation theory into the assessment of cybersecurity awareness, this study provides comprehensive measurements of the awareness of both threats and available countermeasures. Moreover, the influence of GSM on cybersecurity awareness among organizational insiders is investigated to provide insights into the effectiveness of recent government efforts to promote cybersecurity. Finally, by considering the information security context of the public sector, this research provides a foundation for the top management of public organizations to make strategic decisions about the governance, use and operation of computer systems and networks.
The remainder of the study is structured as follows. Section 2 reviews the literature and presents the theoretical framework, variable definitions, proposed hypotheses and the research model. Section 3 outlines the methodology for addressing the research questions, while Section 4 provides the results and discussion. Section 5 concludes with theoretical contributions, research implications and limitations.
2. Literature review
2.1 Protection motivation theory
The PMT is a widely acknowledged theoretical framework for evaluating behaviors intended to mitigate the adverse consequences of perceived threats (Li et al., 2022). This theory explains that attitude change is contingent on the level of protective motivation generated from the cognitive appraisal process, which includes perceived severity, perceived vulnerability, self-efficacy and response efficacy (Maddux and Rogers, 1983). Perceived severity refers to the perceived magnitude, danger and consequences of a manifest threat such as computer viruses, unauthorized access or internet hacking (Hina et al., 2019; Li et al., 2022). Perceived vulnerability reflects an individual's perception of the likelihood of a threat occurring or of being exposed to a threat (Hina et al., 2019; Li et al., 2019; Wong et al., 2022). Self-efficacy pertains to an individual's judgment of the capabilities and skills required to execute recommended protective behaviors for coping with threats, such as eliminating spyware from electronic devices or handling virus-infected files (Hina et al., 2019; Li et al., 2022). Response efficacy relates to the perceived effectiveness of countermeasures against cyberattacks that an employee can implement to prevent a potential threat (Hina et al., 2019; Li et al., 2019; Wong et al., 2022).
The PMT was originally developed in the health domain (Floyd et al., 2000) but has since been extended to other fields, including computer and information security (Boss et al., 2015). The PMT has been used to explain general users’ predominant information security behaviors (van Bavel et al., 2019). It has also been used to analyze individual information security practices in various settings, such as households (Martens et al., 2019), higher education organizations (Hina et al., 2019; Hina and Dominic, 2020) and business organizations (Li et al., 2019). The PMT is especially advantageous in the organizational context, where employees and end-users require additional encouragement to safeguard their valuable data assets (Li et al., 2022). Here, we use the PMT to investigate the determinants of protective behaviors among public servants in governmental organizations, an understudied segment.
2.2 Cultivation theory
Cultivation theory is a communication theory that describes how mass media coverage shapes the public’s opinions of social phenomena (Gerbner and Gross, 1976). Cultivation theory posits that a persistently high frequency of media consumption will increase the alignment of an individual’s perceptions of social realities with media depictions (Tang et al., 2021). Cultivation is a continual and dynamic process that includes two forms: mainstreaming and resonance (Hermann et al., 2020). Mainstreaming refers to the convergence of different views as a result of content exposure, while resonance occurs when media content is highly relevant to real-life experiences (Hermann et al., 2020). The cultivation approach originally focused on television but can be applied to any dominant medium, especially social media, that strengthens perceptions and attitudes by providing an accessible, engaging and shared symbolic environment (Intravia et al., 2017). GSM has attracted attention as a means of cultivation (Tang et al., 2021). Compared to conventional government Web portals, social media is a more efficient means of distributing information and fostering two-way interaction (Guo et al., 2021).
Both the PMT and cultivation theory are suitable for this study. This study expands the scope of these theories to examine civil servants’ assessment of cybersecurity awareness and protective behavior.
2.3 Hypothesis development
2.3.1 Cybersecurity awareness, information protection motivation and employee protective behavior.
Although research on cybersecurity awareness is growing, there is no single construct; researchers have considered several dimensions of cybersecurity awareness (Hanus et al., 2018). Defining cybersecurity awareness is a prerequisite for increasing cybersecurity awareness (Zwilling et al., 2022). Several prior studies have used the PMT to conceptualize cybersecurity awareness but have not explicitly defined the construct (Lee and Larsen, 2009; Vance et al., 2012). In this study, we adopt a threat perspective and consider cybersecurity awareness a second-order construct comprising four components: perceived severity, perceived vulnerability, self-efficacy and response efficacy. Thus, cybersecurity awareness is the state where employees are conscious of the occurrence and nature of cybersecurity threats, the potential effects of cybersecurity threats on organizational security (perceived severity and perceived vulnerability), their own capabilities and the expected measures for preventing such threats (self-efficacy and response efficacy).
According to the PMT, the level of elicited protection motivation is contingent on appraisals of perceived severity, perceived vulnerability, self-efficacy and response efficacy (Maddux and Rogers, 1983). If a threat is perceived as non-severe or improbable, if no viable action can be implemented to mitigate it or if the individual doubts their ability to cope with the situation, then protection motivation will not be aroused, and behavioral intentions will not change. Therefore, cybersecurity awareness should have a direct influence on the motivation for protective action:
Cybersecurity awareness has a positive impact on information protection motivation.
According to the PMT, employees who are more aware of cyberthreats are more likely to learn how to secure their devices, leading to stronger cyber-protective behavior (Klein and Zwilling, 2023). Examples of protective behaviors include regularly changing passwords, adhering to organizational standards, exercising caution before clicking on links from unknown sources, backing up data, patching software and deploying cybersecurity defense tools (Posey et al., 2015; Tang et al., 2021). By contrast, risky behaviors include activities such as disclosing personal passwords, downloading unlawful content, violating copyright regulations and neglecting suggested software updates (Zwilling et al., 2022). Previous research has shown direct effects of cybersecurity awareness on the prevention of information system misuse (D’Arcy et al., 2009) and compliance with cybersecurity policy (Bulgurcu et al., 2010). High cybersecurity awareness significantly increases employees’ knowledge of security threats and system vulnerabilities and, in turn, their vigilance against potential cyberattacks, thus ensuring that the information, systems and networks they engage with are protected (Corallo et al., 2022). The greater the perceived severity and perceived vulnerability of a potential threat to their organization’s cyber assets, the greater the likelihood that employees will adopt protective behaviors and vice versa (Martens et al., 2019). Likewise, if an employee has strong confidence in a coping mechanism’s effectiveness and their ability to execute that protective measure, then they will be more inclined to act (Li et al., 2022; Tang et al., 2021). Thus, we propose the following:
Cybersecurity awareness has a positive impact on employee protective behavior.
2.3.2 Information protection motivation and employee protective behavior
Some scholars have reframed information protection motivation as an attitude, while others omit information protection motivation and directly examine the predictive value of (intention toward) protective behavior (Wu, 2020). Few studies have examined the link between protection motivation and actual behaviors. While the primary aim of the PMT is to assess protection motivation, it can be extended to evaluate actual protective behaviors (Ma, 2022). As the ultimate goal of cybersecurity research is to enhance security practices instead of merely intentions, assessing actual behaviors is valuable. In addition, a meta-analysis of the PMT showed that protection motivation is the strongest predictor of behavioral changes (Boss et al., 2015). Thus, we extend the PMT by integrating employee protective behavior and hypothesize the following:
Information protection motivation has a positive impact on employee protective behavior.
2.3.3 Government social media and cybersecurity awareness
According to cultivation theory, media consumption can shape an individual’s perceptions and opinions (Hermann et al., 2020). GSM participation encompasses the interactive engagement of GSM followers through behaviors such as viewing, commenting and exchanging cybersecurity-related messages inside the GSM network (Tang et al., 2021). GSM participation can be seen as a form of media consumption because it contributes to enhancing people’s situational awareness of a cyber crisis (Guo et al., 2021). Individuals who actively engage with GSM messages regarding cybersecurity are more likely to develop heightened cybersecurity awareness (Tang et al., 2021). More precisely, the government's regular dissemination of cybercrime-related news frequently results in elevated levels of perceived threat among the public. This is because individuals tend to believe that events shown in the media have the potential to impact them or their loved ones (Intravia et al., 2017; Shah et al., 2020). Moreover, participation in GSM equips individuals with timely information and guidance to respond effectively to potential threats (Farooq et al., 2020), providing a foundation for evaluating the efficacy of protective responses (Tu et al., 2015). In addition, this advanced preparedness will increase individuals’ confidence in their ability to protect themselves from threats (Tang et al., 2021). Thus, we propose the following:
Government social media has a positive impact on cybersecurity awareness.
For an individual to be motivated to take an action, they must understand the purpose of the action, recognize its significance and be aware of the expectations associated with it (Chen et al., 2018). GSM participation can shape an individual’s perceptions and opinions (Guo et al., 2021). Tang et al. (2021) found that engaging in GSM contributes positively to individuals’ motivation to adopt protective measures against cyber scams via perceived severity, perceived vulnerability, self-efficacy and response efficacy. Based on these arguments, the following is proposed:
Government social media has a positive impact on information protection motivation.
2.3.4 Organizational policy compliance, cybersecurity awareness and employee protective behavior
On the basis of the PMT framework, it can be inferred that individuals who possess greater awareness of cyberthreats are more likely to actively seek out information on securing their devices (Klein and Zwilling, 2023). This heightened awareness is likely to increase compliance with organizational policy. Organizational policy compliance is widely believed to significantly influence employees’ behaviors and enhance an organization’s information security level (Chen et al., 2018). A cybersecurity policy with an understandable rationale can influence protective behaviors (D’Arcy et al., 2009; Safa et al., 2015). However, several scholars argue that awareness of cybersecurity policy, not the content of the cybersecurity policy itself, significantly influences computer misuse intentions and abuse behaviors such as modifying, stealing or destroying software and data (Lee et al., 2004; Lee and Larsen, 2009). Indeed, raising employees’ awareness of security policies positively contributes to their beliefs about cybersecurity and their behavior in protecting information security (Li et al., 2019). Because previous results are contradictory, in this study, we reinvestigate the relationship between organizational policy compliance and employee protective behavior in the specific context of governmental organizations:
Organizational policy compliance has a positive impact on cybersecurity awareness.
Organizational policy compliance has a positive impact on employee protective behavior.
Figure 1 compiles the hypotheses into the research model.
3. Methodology
3.1 Measurement
All constructs were assessed using a seven-point Likert scale ranging from 1 (strongly disagree) to 7 (strongly agree). The measurement items on the questionnaire were adapted from previous studies with minor or major modifications. The first part of the survey collected demographic information such as gender, age, education level, working tenure and organizational size. The second section included the constructs and their corresponding measurement items. The indicators for organizational policy compliance and perceived severity were adapted from Hina et al. (2019). The measures for perceived vulnerability and response efficacy were drawn from previous studies (Hina et al., 2019; Li et al., 2019; Wong et al., 2022). Self-efficacy was measured using items adapted from Hina et al. (2019) and Li et al. (2022). The GSM items were adapted from Tang et al. (2021). Information protection motivation was evaluated using measurement scales from Ma (2022) and Posey et al. (2015). The measures of employees' protective behaviors were adapted from Bulgurcu et al. (2010) and Wong et al. (2022). Table A1 in the Appendix describes the measurement of all variables.
Measurement items
| Construct (source) . | Code . | Measurement items . | Modifications . |
|---|---|---|---|
| Organizational policy compliance (Hina et al., 2019) | OPC1 | My organization has established rules of behavior for computer use to comply with governmental regulations | Major modification |
| OPC2 | My organization has specific guidelines for computer use to comply with governmental regulations | Major modification | |
| OPC3 | My organization has a policy that forbids employees from accessing certain online websites when their computers contain confidential documents to comply with governmental regulations | Major modification | |
| OPC4 | My organization has defined code(s) of conduct explaining the do’s and don’ts of information security to comply with governmental regulations | Major modification | |
| Perceived severity (Hina et al., 2019) | PS1 | Protecting my organization’s information is important | Minor modification |
| PS2 | At work, having my confidential information accessed without my consent or knowledge can be a serious problem for me | No change | |
| PS3 | I understand that having someone successfully breach or damage my information resources at work is very dangerous | No change | |
| PS4 | Loss of data because of hackers is a serious problem for me | Major modification | |
| PS5 | Organizing staff training will be a critical first step to ensure information security | Major modification | |
| PS6 | Risks can be reduced as employees become more aware of the threats and consequences stemming from their negligence | Major modification | |
| PS7 | Through education, the provision of sufficient data and supporting information helps increase employees’ cybersecurity awareness | Major modification | |
| Perceived vulnerability (Hina et al., 2019; Li et al., 2019; Wong et al., 2022) | PV1 | I know that my organization could be vulnerable to security breaches if I do not adhere to its Information Security Policies | No change |
| PV2 | I may fall victim to a malicious attack if I fail to comply with my organization’s Information Security Policies | No change | |
| PV3 | In terms of information security risks at work, my computing resources can be vulnerable | No change | |
| PV4 | I believe that every individual who is conscious and makes efforts to protect the organization's information will reduce the risk of illegal access | Major modification | |
| PV5 | Organizations should invest in using modern cybersecurity technologies | Major modification | |
| PV6 | Organizations need to inform employees about potential cybersecurity threats regularly | Major modification | |
| PV7 | It is likely that a potential information security violation will occur to my organization’s information systems | Major modification | |
| Self-efficacy (Hina et al., 2019; Li et al., 2022) | SE1 | I believe that I have the necessary skills to protect myself from information security violations | No change |
| SE2 | I believe that I have developed the capability to prevent people from getting my confidential information | No change | |
| SE3 | I enable security measures (firewall, antivirus, etc.) on my work computing resources | No change | |
| SE4 | I believe that protecting myself from information security violations is within my control | Major modification | |
| SE5 | I feel confident in setting the Web browser to different security levels | No change | |
| SE6 | I feel confident in handling virus-infected files | No change | |
| SE7 | I feel confident in getting rid of spyware and malware from my computer | No change | |
| Response efficacy (Hina et al., 2019; Li et al., 2019; Wong et al., 2022) | RE1 | In my organization, efforts to ensure the safety of my confidential information are effective | No change |
| RE2 | In my organization, the available security measures to protect my work information from security violations are effective | No change | |
| RE3 | The preventive measures available to me at my organization to deal with malicious content are effective | No change | |
| RE4 | Security measures at my organization prevent hackers from gaining access to sensitive personal or educational information | No change | |
| RE5 | Complying with the information security policies in my organization will keep security breaches down | No change | |
| RE6 | If I comply with information security policies, then the chance of information security breaches occurring will be reduced | No change | |
| RE7 | Careful compliance with information security policies helps to avoid security problems | No change | |
| RE8 | Organizations can improve information security by showing their employees how security negligence can impact the security posture of an organization | Major modification | |
| RE9 | Organizations should have a General Data Protection Regulation | Minor modification | |
| RE10 | Organizations should upgrade antivirus and firewall software | Minor modification | |
| Government social media (Tang et al., 2021) | GSM1 | I always read and listen to cybersecurity recommendations posted by the GSM | Major modification |
| GSM2 | I always share cybersecurity recommendations posted by the GSM | Major modification | |
| GSM3 | I always communicate cybersecurity recommendations posted by the GSM | Major modification | |
| Information protection motivation (Ma, 2022; Posey et al., 2015) | IPM1 | I intend to protect my organization from its information security threats | No change |
| IPM2 | My organization’s success level in preventing information security threats is very high | Major modification | |
| IPM3 | I am always willing to engage in activities that protect my organization’s information systems from security threats | Major modification | |
| IPM4 | I always expend effort to protect my organization from its information security threats | Major modification | |
| IPM5 | I intend to try my best to prevent information security threats from happening in my organization | No change | |
| Employee protective behavior (Li et al., 2019) | EPB1 | I keep the anti-virus software on my computer up-to-date | No change |
| EPB2 | I watch for unusual computer behaviors/responses (e.g. computer slowing down or freezing up, pop-up windows, etc.) | No change | |
| EPB3 | I am always concerned about any malware that is reported through media channels | Major modification |
| Construct (source) . | Code . | Measurement items . | Modifications . |
|---|---|---|---|
| Organizational policy compliance (Hina et al., 2019) | OPC1 | My organization has established rules of behavior for computer use to comply with governmental regulations | Major modification |
| OPC2 | My organization has specific guidelines for computer use to comply with governmental regulations | Major modification | |
| OPC3 | My organization has a policy that forbids employees from accessing certain online websites when their computers contain confidential documents to comply with governmental regulations | Major modification | |
| OPC4 | My organization has defined code(s) of conduct explaining the do’s and don’ts of information security to comply with governmental regulations | Major modification | |
| Perceived severity (Hina et al., 2019) | PS1 | Protecting my organization’s information is important | Minor modification |
| PS2 | At work, having my confidential information accessed without my consent or knowledge can be a serious problem for me | No change | |
| PS3 | I understand that having someone successfully breach or damage my information resources at work is very dangerous | No change | |
| PS4 | Loss of data because of hackers is a serious problem for me | Major modification | |
| PS5 | Organizing staff training will be a critical first step to ensure information security | Major modification | |
| PS6 | Risks can be reduced as employees become more aware of the threats and consequences stemming from their negligence | Major modification | |
| PS7 | Through education, the provision of sufficient data and supporting information helps increase employees’ cybersecurity awareness | Major modification | |
| Perceived vulnerability (Hina et al., 2019; Li et al., 2019; Wong et al., 2022) | PV1 | I know that my organization could be vulnerable to security breaches if I do not adhere to its Information Security Policies | No change |
| PV2 | I may fall victim to a malicious attack if I fail to comply with my organization’s Information Security Policies | No change | |
| PV3 | In terms of information security risks at work, my computing resources can be vulnerable | No change | |
| PV4 | I believe that every individual who is conscious and makes efforts to protect the organization's information will reduce the risk of illegal access | Major modification | |
| PV5 | Organizations should invest in using modern cybersecurity technologies | Major modification | |
| PV6 | Organizations need to inform employees about potential cybersecurity threats regularly | Major modification | |
| PV7 | It is likely that a potential information security violation will occur to my organization’s information systems | Major modification | |
| Self-efficacy (Hina et al., 2019; Li et al., 2022) | SE1 | I believe that I have the necessary skills to protect myself from information security violations | No change |
| SE2 | I believe that I have developed the capability to prevent people from getting my confidential information | No change | |
| SE3 | I enable security measures (firewall, antivirus, etc.) on my work computing resources | No change | |
| SE4 | I believe that protecting myself from information security violations is within my control | Major modification | |
| SE5 | I feel confident in setting the Web browser to different security levels | No change | |
| SE6 | I feel confident in handling virus-infected files | No change | |
| SE7 | I feel confident in getting rid of spyware and malware from my computer | No change | |
| Response efficacy (Hina et al., 2019; Li et al., 2019; Wong et al., 2022) | RE1 | In my organization, efforts to ensure the safety of my confidential information are effective | No change |
| RE2 | In my organization, the available security measures to protect my work information from security violations are effective | No change | |
| RE3 | The preventive measures available to me at my organization to deal with malicious content are effective | No change | |
| RE4 | Security measures at my organization prevent hackers from gaining access to sensitive personal or educational information | No change | |
| RE5 | Complying with the information security policies in my organization will keep security breaches down | No change | |
| RE6 | If I comply with information security policies, then the chance of information security breaches occurring will be reduced | No change | |
| RE7 | Careful compliance with information security policies helps to avoid security problems | No change | |
| RE8 | Organizations can improve information security by showing their employees how security negligence can impact the security posture of an organization | Major modification | |
| RE9 | Organizations should have a General Data Protection Regulation | Minor modification | |
| RE10 | Organizations should upgrade antivirus and firewall software | Minor modification | |
| Government social media (Tang et al., 2021) | GSM1 | I always read and listen to cybersecurity recommendations posted by the GSM | Major modification |
| GSM2 | I always share cybersecurity recommendations posted by the GSM | Major modification | |
| GSM3 | I always communicate cybersecurity recommendations posted by the GSM | Major modification | |
| Information protection motivation (Ma, 2022; Posey et al., 2015) | IPM1 | I intend to protect my organization from its information security threats | No change |
| IPM2 | My organization’s success level in preventing information security threats is very high | Major modification | |
| IPM3 | I am always willing to engage in activities that protect my organization’s information systems from security threats | Major modification | |
| IPM4 | I always expend effort to protect my organization from its information security threats | Major modification | |
| IPM5 | I intend to try my best to prevent information security threats from happening in my organization | No change | |
| Employee protective behavior (Li et al., 2019) | EPB1 | I keep the anti-virus software on my computer up-to-date | No change |
| EPB2 | I watch for unusual computer behaviors/responses (e.g. computer slowing down or freezing up, pop-up windows, etc.) | No change | |
| EPB3 | I am always concerned about any malware that is reported through media channels | Major modification |
3.2 Data collection
The survey was initially written in English and subsequently translated into Vietnamese to facilitate its distribution to a wider range of participants. A pilot study of 30 respondents was performed to assess the appropriateness of the translation in the Vietnamese context. Based on the results, modifications were made to improve the clarity and readability of the questionnaire. From October 2022 to March 2023, data were collected by distributing the survey to public servants working at governmental organizations. We received invaluable support from local authorities to distribute the survey in their organizations.
The data were collected by applying nonprobability methods, specifically, a stratification approach. According to this approach, questionnaires were sent to 200 public personnel in each region of Ho Chi Minh City and Hanoi Capital. In addition, 150 surveys were disseminated in two adjacent provinces: Dong Nai Province and Binh Duong Province. In total, 700 questionnaires were distributed, and 564 were returned, of which 330 responses were valid.
3.3 Methodology
Partial least squares–structural equation modeling (PLS–SEM) was used to analyze the data and evaluate the research model. PLS–SEM is a variance-based approach that assesses partial model structures by integrating principal component analysis and ordinary least squares regression (Hair et al., 2020). PLS–SEM is widely used in several disciplines, including research on cybersecurity behaviors (Alanazi et al., 2022; Wong et al., 2022). PLS–SEM aligns well with our research objectives for several reasons. First, it can test a theoretical framework from a predictive standpoint. Second, it provides support for the structural model, which is complex and encompasses numerous constructs, indicators, dependent components and model relationships. Finally, it enhances comprehension when exploring extensions of established theories (Hair et al., 2019).
4. Results
4.1 Demographic characteristics
The demographic profile and organizational characteristics of the respondents are shown in Table 1. Among the respondents, 26.67% are men, and 74.0% are women. The majority (71.21%) are 18–35 years old. Over 72% of the participants possess a bachelor’s degree or higher, 66.97% have more than five years of working experience and 52.42% work at large organizations with more than 100 employees.
Characteristics of the respondents
| Demographic items . | Frequency (n = 330) . | % . |
|---|---|---|
| Gender | ||
| Female | 88 | 26.67 |
| Male | 242 | 73.33 |
| Age | ||
| 18–35 years | 235 | 71.21 |
| 36–45 years | 73 | 22.12 |
| Over 45 years | 22 | 6.67 |
| Education level | ||
| High school | 90 | 27.27 |
| Undergraduate | 185 | 56.06 |
| Postgraduate | 55 | 16.67 |
| Working experience | ||
| Less than 3 years | 49 | 14.85 |
| 3–5 years | 60 | 18.18 |
| More than 5 years | 221 | 66.97 |
| Organizational size | ||
| Fewer than 50 employees | 98 | 29.70 |
| 51–100 employees | 59 | 17.88 |
| More than 100 employees | 173 | 52.42 |
| Demographic items . | Frequency (n = 330) . | % . |
|---|---|---|
| Gender | ||
| Female | 88 | 26.67 |
| Male | 242 | 73.33 |
| Age | ||
| 18–35 years | 235 | 71.21 |
| 36–45 years | 73 | 22.12 |
| Over 45 years | 22 | 6.67 |
| Education level | ||
| High school | 90 | 27.27 |
| Undergraduate | 185 | 56.06 |
| Postgraduate | 55 | 16.67 |
| Working experience | ||
| Less than 3 years | 49 | 14.85 |
| 3–5 years | 60 | 18.18 |
| More than 5 years | 221 | 66.97 |
| Organizational size | ||
| Fewer than 50 employees | 98 | 29.70 |
| 51–100 employees | 59 | 17.88 |
| More than 100 employees | 173 | 52.42 |
4.2 Common method bias
The methodology used in this study raises the risk of common method bias (CMB) because the questionnaire instructions and social desirability may affect the respondents’ answers, leading to shared variation among indicators (Kock, 2015). Full collinearity variance inflation factors (FCVIFs) can effectively detect CMB, even in a model that satisfies the standard criteria for convergent and discriminant validity based on confirmatory factor analysis (Kock, 2015). If all FCVIFs obtained through a full collinearity test are 3.3 or less, then the model is considered free from CMB (Kock, 2015). As shown in Table 3, the FCVIFs for all latent constructs are below the 3.3 threshold, implying that the collected data are unaffected by CMB.
HTMT ratio and Fornell–Larcker criterion
| Constructs . | EPB . | OPC . | GMS . | IPM . | PS . | PV . | RE . | SE . |
|---|---|---|---|---|---|---|---|---|
| HTMT ratio | ||||||||
| Employee protective behavior (EPB) | ||||||||
| Organizational policy compliance (OPC) | 0.745 | |||||||
| Government social media (GSM) | 0.855 | 0.849 | ||||||
| Information protection motivation (IPM) | 0.864 | 0.761 | 0.799 | |||||
| Perceived severity (PS) | 0.667 | 0.594 | 0.601 | 0.728 | ||||
| Perceived vulnerability (PV) | 0.457 | 0.417 | 0.394 | 0.473 | 0.592 | |||
| Response efficacy (RE) | 0.743 | 0.820 | 0.760 | 0.827 | 0.747 | 0.514 | ||
| Self-efficacy (SE) | 0.724 | 0.684 | 0.719 | 0.688 | 0.531 | 0.488 | 0.813 | |
| Fornell–Larcker criterion | ||||||||
| Employee protective behavior (EPB) | 0.925 | |||||||
| Organizational policy compliance (OPC) | 0.685 | 0.904 | ||||||
| Government social media (GSM) | 0.775 | 0.773 | 0.912 | |||||
| Information protection motivation (IPM) | 0.805 | 0.713 | 0.737 | 0.908 | ||||
| Perceived severity (PS) | 0.615 | 0.550 | 0.549 | 0.682 | 0.828 | |||
| Perceived vulnerability (PV) | 0.420 | 0.387 | 0.359 | 0.440 | 0.540 | 0.794 | ||
| Response efficacy (RE) | 0.695 | 0.766 | 0.703 | 0.782 | 0.691 | 0.472 | 0.818 | |
| Self-efficacy (SE) | 0.671 | 0.640 | 0.663 | 0.650 | 0.501 | 0.457 | 0.775 | 0.863 |
| Constructs . | EPB . | OPC . | GMS . | IPM . | PS . | PV . | RE . | SE . |
|---|---|---|---|---|---|---|---|---|
| HTMT ratio | ||||||||
| Employee protective behavior (EPB) | ||||||||
| Organizational policy compliance (OPC) | 0.745 | |||||||
| Government social media (GSM) | 0.855 | 0.849 | ||||||
| Information protection motivation (IPM) | 0.864 | 0.761 | 0.799 | |||||
| Perceived severity (PS) | 0.667 | 0.594 | 0.601 | 0.728 | ||||
| Perceived vulnerability (PV) | 0.457 | 0.417 | 0.394 | 0.473 | 0.592 | |||
| Response efficacy (RE) | 0.743 | 0.820 | 0.760 | 0.827 | 0.747 | 0.514 | ||
| Self-efficacy (SE) | 0.724 | 0.684 | 0.719 | 0.688 | 0.531 | 0.488 | 0.813 | |
| Fornell–Larcker criterion | ||||||||
| Employee protective behavior (EPB) | 0.925 | |||||||
| Organizational policy compliance (OPC) | 0.685 | 0.904 | ||||||
| Government social media (GSM) | 0.775 | 0.773 | 0.912 | |||||
| Information protection motivation (IPM) | 0.805 | 0.713 | 0.737 | 0.908 | ||||
| Perceived severity (PS) | 0.615 | 0.550 | 0.549 | 0.682 | 0.828 | |||
| Perceived vulnerability (PV) | 0.420 | 0.387 | 0.359 | 0.440 | 0.540 | 0.794 | ||
| Response efficacy (RE) | 0.695 | 0.766 | 0.703 | 0.782 | 0.691 | 0.472 | 0.818 | |
| Self-efficacy (SE) | 0.671 | 0.640 | 0.663 | 0.650 | 0.501 | 0.457 | 0.775 | 0.863 |
4.3 Validity and reliability
The construct measures’ validity and reliability test statistics are presented in Tables 2 and 3. Factor loadings exceeding 0.70 are recommended to ensure acceptable item reliability (Hair et al., 2020). As shown in Table 3, all indicators exhibit factor loadings exceeding this threshold except RE10, which has a factor loading of 0.662. Thus, RE10 was eliminated from the analysis.
Factor analysis with reliability and validity statistics
| Constructs . | Item no. . | Loadings (> 0.7) . | α (> 0.7) . | CR (> 0.7) . | AVE (> 0.5) . | FCVIF (< 3.3) . |
|---|---|---|---|---|---|---|
| Employee protective behavior (EPB) | EPB1 | 0.918 | 0.915 | 0.917 | 0.855 | 2.880 |
| EPB2 | 0.936 | |||||
| EPB3 | 0.920 | |||||
| Government social media (GSM) | GSM1 | 0.911 | 0.899 | 0.899 | 0.831 | 3.255 |
| GSM2 | 0.919 | |||||
| GSM3 | 0.905 | |||||
| Information protection motivation (IPM) | IPM1 | 0.895 | 0.947 | 0.947 | 0.825 | 1.106 |
| IPM2 | 0.892 | |||||
| IPM3 | 0.903 | |||||
| IPM4 | 0.932 | |||||
| IPM5 | 0.920 | |||||
| Organizational policy compliance (OPC) | OPC1 | 0.893 | 0.926 | 0.927 | 0.818 | 2.182 |
| OPC2 | 0.933 | |||||
| OPC3 | 0.872 | |||||
| OPC4 | 0.919 | |||||
| Cybersecurity awareness (second-order variable) | ||||||
| Perceived severity (PS) | PS1 | 0.845 | 0.924 | 0.926 | 0.686 | 1.838 |
| PS2 | 0.818 | |||||
| PS3 | 0.802 | |||||
| PS4 | 0.847 | |||||
| PS5 | 0.811 | |||||
| PS6 | 0.825 | |||||
| PS7 | 0.850 | |||||
| Perceived vulnerability (PV) | PV1 | 0.796 | 0.903 | 0.906 | 0.631 | 1.484 |
| PV2 | 0.792 | |||||
| PV3 | 0.815 | |||||
| PV4 | 0.776 | |||||
| PV5 | 0.785 | |||||
| PV6 | 0.782 | |||||
| PV7 | 0.814 | |||||
| Response efficacy (RE) | RE1 | 0.873 | 0.938 | 0.942 | 0.670 | 2.516 |
| RE2 | 0.865 | |||||
| RE3 | 0.841 | |||||
| RE4 | 0.828 | |||||
| RE5 | 0.795 | |||||
| RE6 | 0.805 | |||||
| RE7 | 0.801 | |||||
| RE8 | 0.841 | |||||
| RE9 | 0.705 | |||||
| RE10 | Eliminated | |||||
| Self-efficacy (SE) | SE1 | 0.847 | 0.943 | 0.944 | 0.745 | 2.475 |
| SE2 | 0.898 | |||||
| SE3 | 0.824 | |||||
| SE4 | 0.895 | |||||
| SE5 | 0.908 | |||||
| SE6 | 0.827 | |||||
| SE7 | 0.836 | |||||
| Constructs . | Item no. . | Loadings (> 0.7) . | α (> 0.7) . | CR (> 0.7) . | AVE (> 0.5) . | FCVIF (< 3.3) . |
|---|---|---|---|---|---|---|
| Employee protective behavior (EPB) | EPB1 | 0.918 | 0.915 | 0.917 | 0.855 | 2.880 |
| EPB2 | 0.936 | |||||
| EPB3 | 0.920 | |||||
| Government social media (GSM) | GSM1 | 0.911 | 0.899 | 0.899 | 0.831 | 3.255 |
| GSM2 | 0.919 | |||||
| GSM3 | 0.905 | |||||
| Information protection motivation (IPM) | IPM1 | 0.895 | 0.947 | 0.947 | 0.825 | 1.106 |
| IPM2 | 0.892 | |||||
| IPM3 | 0.903 | |||||
| IPM4 | 0.932 | |||||
| IPM5 | 0.920 | |||||
| Organizational policy compliance (OPC) | OPC1 | 0.893 | 0.926 | 0.927 | 0.818 | 2.182 |
| OPC2 | 0.933 | |||||
| OPC3 | 0.872 | |||||
| OPC4 | 0.919 | |||||
| Cybersecurity awareness (second-order variable) | ||||||
| Perceived severity (PS) | PS1 | 0.845 | 0.924 | 0.926 | 0.686 | 1.838 |
| PS2 | 0.818 | |||||
| PS3 | 0.802 | |||||
| PS4 | 0.847 | |||||
| PS5 | 0.811 | |||||
| PS6 | 0.825 | |||||
| PS7 | 0.850 | |||||
| Perceived vulnerability (PV) | PV1 | 0.796 | 0.903 | 0.906 | 0.631 | 1.484 |
| PV2 | 0.792 | |||||
| PV3 | 0.815 | |||||
| PV4 | 0.776 | |||||
| PV5 | 0.785 | |||||
| PV6 | 0.782 | |||||
| PV7 | 0.814 | |||||
| Response efficacy (RE) | RE1 | 0.873 | 0.938 | 0.942 | 0.670 | 2.516 |
| RE2 | 0.865 | |||||
| RE3 | 0.841 | |||||
| RE4 | 0.828 | |||||
| RE5 | 0.795 | |||||
| RE6 | 0.805 | |||||
| RE7 | 0.801 | |||||
| RE8 | 0.841 | |||||
| RE9 | 0.705 | |||||
| RE10 | Eliminated | |||||
| Self-efficacy (SE) | SE1 | 0.847 | 0.943 | 0.944 | 0.745 | 2.475 |
| SE2 | 0.898 | |||||
| SE3 | 0.824 | |||||
| SE4 | 0.895 | |||||
| SE5 | 0.908 | |||||
| SE6 | 0.827 | |||||
| SE7 | 0.836 | |||||
Internal consistency reliability can be assessed using both Cronbach's alpha (α) and composite reliability (CR); values greater than 0.70 are recommended for both reliability measures (Hair et al., 2020). Table 3 shows that all constructs have both α and CR values above 0.70, indicating satisfactory to good reliability.
An average variance extracted (AVE) value of 0.50 or greater signifies that the construct accounts for at least 50% of the variance in its items (Hair et al., 2020). In this study, all AVE values of the constructs are higher than 0.50, implying that the convergent validity test is satisfied.
Finally, discriminant validity was tested by using the heterotrait–monotrait (HTMT) ratio and Fornell–Larcker criterion (Hair et al., 2020). HTMT ratio compares the correlations of an item across constructs to its correlations with the same construct, and an upper boundary of 0.85 or 0.90 (Hair et al., 2019) is suggested to avoid discriminant validity issues. The Fornell–Larcker criterion is fulfilled when a factor’s squared AVE exceeds the square root of its inter-construct correlations (Fornell and Larcker, 1981). As shown in Table 4, all constructs meet the requirements for both the HTMT ratio and Fornell–Larcker criterion, implying acceptable levels of discriminant validity.
Hypothesis testing results
| Hypothesis . | β . | t-value . | p-value . | Remarks . | |
|---|---|---|---|---|---|
| H1 | CSA → EPB | 0.188 | 2.335 | 0.020 | Supported |
| H2 | CSA → IPM | 0.493 | 7.161 | 0.000 | Supported |
| H3 | GSM → CSA | 0.359 | 4.102 | 0.000 | Supported |
| H4 | GSM → IPM | 0.379 | 4.918 | 0.000 | Supported |
| H5 | IPM → EPB | 0.555 | 6.025 | 0.000 | Supported |
| H6 | OPC → CSA | 0.476 | 6.023 | 0.000 | Supported |
| H7 | OPC → EPB | 0.148 | 1.592 | 0.111 | Not supported |
| Hypothesis . | β . | t-value . | p-value . | Remarks . | |
|---|---|---|---|---|---|
| H1 | CSA → EPB | 0.188 | 2.335 | 0.020 | Supported |
| H2 | CSA → IPM | 0.493 | 7.161 | 0.000 | Supported |
| H3 | GSM → CSA | 0.359 | 4.102 | 0.000 | Supported |
| H4 | GSM → IPM | 0.379 | 4.918 | 0.000 | Supported |
| H5 | IPM → EPB | 0.555 | 6.025 | 0.000 | Supported |
| H6 | OPC → CSA | 0.476 | 6.023 | 0.000 | Supported |
| H7 | OPC → EPB | 0.148 | 1.592 | 0.111 | Not supported |
Notes:
CSA = Cybersecurity awareness; EPB = Employee protective behavior; IPM = Information protection motivation; GSM = Government social media; OPC = Organizational policy compliance
4.4 Structural model assessment
As there is no standard goodness-of-fit statistic for PLS–SEM, the quality of the model is evaluated based on its capacity to predict the endogenous constructs (Hair et al., 2019). This evaluation is guided by the coefficient of determination (R2) and the effect size (f 2) (Hair et al., 2019).
R2 indicates the collective impact of the exogenous variables on the endogenous variables and ranges from 0 to 1, with 1 indicating absolute predictive accuracy (Hair et al., 2019). R2 values of 0.75, 0.50 and 0.25 are interpreted as indicating substantial, moderate and weak predictive accuracy, respectively (Hair et al., 2019). In our model, the R2 values of the three endogenous variables – cybersecurity awareness, information protection motivation and employee protective behavior – are 0.614, 0.654 and 0.682, respectively. These values indicate moderate to substantial predictive accuracy.
f 2 is used to evaluate the effect of removing a specific predictor construct on the R 2 of an endogenous variable (Hair et al., 2019). f 2 values of 0.02, 0.15 and 0.35 indicate small, medium and large effect sizes, respectively. The relationships investigated in this study have medium or large effect sizes, excluding the relationships between cybersecurity awareness and employee protective behavior and between organizational policy compliance and employee protective behavior, which have f2 values of 0.031 and 0.028, respectively.
4.5 Hypothesis testing
The hypothesis testing results are presented in Table 4. A hypothesis is accepted when the p-value is ≤ 0.05 or the corresponding t-value is >1.96; otherwise, it is rejected. All hypotheses are supported, except H7. Cybersecurity awareness positively affects information protection motivation and employee protective behavior (β = 0.501, β = 0.175 and p < 0.05), supporting H1 and H2. GSM positively influences cybersecurity awareness and information protection motivation (β = 0.375, β = 0.365 and p < 0.05); thus, H3 and H4 are accepted. The correlation between information protection motivation and employee protective behavior is significantly positive (β = 0.562 and p = 0.000), supporting H5. Organizational policy compliance strongly enhances cybersecurity awareness (β = 448 and p < 0.05), confirming H6. However, H7, which posits a positive impact of organizational policy compliance on employee protective behavior, is rejected because its p-value of 0.109 and t-value of 1.604 do not meet the recommended thresholds.
4.6 Mediating effects
Indirect effects were evaluated to assess three potential mediating relationships: information protection motivation as a mediator of the relationship between cybersecurity awareness and employee protective behavior; cybersecurity awareness as a mediator of the relationship between GSM and information protection motivation; and cybersecurity awareness as a mediator of the relationship between organizational policy compliance and employee protective behavior. As shown in Table 5, the direct and indirect effects in the first two relationships are significantly positive (β > 0 and p < 0.05). For the third relationship, the direct effect is not supported, but the indirect effect is significantly positive (β = 0.079 and p = 0.05). For the first two relationships, the indirect and direct effects have the same direction, indicating complementary mediation. By contrast, cybersecurity awareness fully mediates the relationship between organizational policy compliance and employee protective behavior.
Mediating effects
| Hypothesis . | Type . | β . | t-value . | p-value . | Remarks . | |
|---|---|---|---|---|---|---|
| H1 | CSA → EPB | Direct | 0.188 | 2.335 | 0.020 | Supported |
| CSA → IPM → EPB | Indirect | 0.274 | 4.947 | 0.000 | Complementary (partial mediation) | |
| H4 | GSM → IPM | Direct | 0.379 | 4.918 | 0.000 | Supported |
| GSM → CSA → IPM | Indirect | 0.177 | 3.487 | 0.000 | Complementary (partial mediation) | |
| H7 | OPC → EPB | Direct | 0.148 | 1.592 | 0.111 | Not supported |
| OPC → CSA → EPB | Indirect | 0.068 | 1.806 | 0.071 | Indirect only (full mediation) | |
| Hypothesis . | Type . | β . | t-value . | p-value . | Remarks . | |
|---|---|---|---|---|---|---|
| H1 | CSA → EPB | Direct | 0.188 | 2.335 | 0.020 | Supported |
| CSA → IPM → EPB | Indirect | 0.274 | 4.947 | 0.000 | Complementary (partial mediation) | |
| H4 | GSM → IPM | Direct | 0.379 | 4.918 | 0.000 | Supported |
| GSM → CSA → IPM | Indirect | 0.177 | 3.487 | 0.000 | Complementary (partial mediation) | |
| H7 | OPC → EPB | Direct | 0.148 | 1.592 | 0.111 | Not supported |
| OPC → CSA → EPB | Indirect | 0.068 | 1.806 | 0.071 | Indirect only (full mediation) | |
4.7 Discussion
This study examines how GSM and organizational policy compliance affect employees' cybersecurity awareness, motivation and behaviors. Our findings substantiate six of the seven proposed hypotheses. Specifically, cybersecurity awareness is found to positively impact information protection motivation and to directly positively influence employee protective behavior, consistent with a previous study (Tang et al., 2021). Wong et al. (2022) also observed that cybersecurity awareness significantly improves employees’ proficiency in handling cybersecurity tasks in response to perceived threats, and awareness has been shown to directly impact cyber-misuse prevention and cybersecurity policy compliance (Bulgurcu et al., 2010; D’Arcy et al., 2009). In addition, a significant positive correlation is observed between information protection motivation and employee protective behavior. This result aligns with the research of Ma (2022), who concluded that protection motivation is a robust predictor of behavior. Information protection motivation also partially mediates the relationship between cybersecurity awareness and employee protective behavior.
GSM has a positive influence on cybersecurity awareness, consistent with prior suggestions that GSM is the primary source of crisis-related information (Intravia et al., 2017; Shah et al., 2020; Tang et al., 2021). Active engagement with GSM not only leads individuals to believe that cyberattack-related media events can affect them but also equips them with the knowledge and preparedness needed to respond effectively, thereby enhancing cybersecurity awareness. Cybersecurity awareness also partially mediates the relationship between GSM and information protection motivation. This observation aligns with the findings of Tang et al. (2021), who claim that social media information consumption motivates users to take preventive actions. By demonstrating a direct impact of GSM on information protection motivation, this study provides a novel perspective, as prior research has predominantly investigated the influence of GSM on motivation and behaviors by measuring variables such as fear of victimization.
Last but not least, organizational policy compliance substantially boosts cybersecurity awareness. However, there is no direct impact of organizational policy compliance on employee protective behavior; instead, this relationship is fully mediated by cybersecurity awareness. Hina et al. (2019) suggested that to enhance security behavior and actions, organizations must go beyond distributing organizational cybersecurity policies and ensuring familiarity with their content; employees must fully perceive the severity of a security breach and the organization's vulnerability to it. The mediating role of cybersecurity awareness underscores the importance of not only formulating a cybersecurity policy but also implementing processes to disseminate and instill it in the minds of employees to enhance protective behaviors.
5. Implications and conclusion
5.1 Theoretical contributions
First, the present study provides a comprehensive analysis of the literature on cybersecurity awareness, motivation and behavior. This study extends the PMT and cultivation theory by incorporating employee protective behavior as a crucial factor and examining the connection between this concept and information protection motivation. Assessing real actions is an essential component of cybersecurity research, as the main objective is to enhance security practices rather than just intentions. This study demonstrates that cybersecurity awareness and information protection motivation both significantly influence employee protective behavior.
Second, this study integrates four cognitive factors (perceived severity, perceived vulnerability, self-efficacy and response efficacy) to create the second-order construct of cybersecurity awareness. This multidimensional construct reflects the complexity of cybersecurity awareness while simplifying the model and reducing the number of hypotheses, allowing us to focus on what truly matters and uncover meaningful insights.
Third, our conceptual framework incorporates the effects of cultivation through GSM to investigate the antecedents of cybersecurity awareness. The literature primarily focuses on understanding why individuals engage with GSM during crises and on categorizing the emergency messaging strategies used by GSM (Tang et al., 2021). These studies neglect the impact of GSM on individuals' awareness of and motivation toward perennially urgent issues such as cybersecurity policy, particularly when individuals enthusiastically engage with cybersecurity content shared on GSM. Our results confirm that GSM positively affects both cybersecurity awareness and information protection motivation.
Finally, there is no consensus in the literature on the effectiveness of cybersecurity policies, particularly their impact on protective behaviors. Therefore, we investigate the direct influence of organizational cybersecurity compliance on protective behavior and its indirect effect through cybersecurity awareness. Our findings indicate that organizational policy compliance does not have a direct impact on employee protective behavior; instead, its influence is mediated by cybersecurity awareness.
5.2 Practical implications
This research provides a robust foundation for senior management of public organizations to formulate strategic solutions addressing deficiencies in the governance, utilization and operation of computer systems and networks. Empirical studies have predominantly focused on the private sector, and the applicability and transferability of the findings to public organizations remain unclear. Public organizations are progressively embracing digitalization to enhance the flow and storage of operational data. However, current organizational policies for managing and using computer systems are insufficient to support these digitalization efforts, increasing the risk of information insecurity.
Organizational policy noncompliance occurs in the public sector when public officials, despite having a fundamental understanding of cybersecurity, fail to comply with agency standards. Cyberspace policy noncompliance, such as using unverified data from USB drives or accessing online resources without permission, can compromise network security and threaten privileged government computer system data. By adopting robust international standards-based laws, government organizations can strengthen their cyber defenses and encourage employee compliance. This will safeguard vital assets and boost government credibility.
Organizational policy compliance also affects employees’ cybersecurity behavior. This study finds that following the law indirectly increases employees' cybersecurity awareness and willingness to take precautions. Organizations must go beyond policies to improve compliance and cybersecurity. They should invest more in training, cybersecurity newsletters and alarm alerts. These activities are essential for effective policy dissemination and employee comprehension of cybersecurity threats and best practices. Organizations can foster a cybersecurity-savvy and regulatory-compliant culture by engaging employees through many channels, which will improve the overall security stance of the organization.
Considering the significant impacts of GSM on cybersecurity awareness and information protection motivation, government organizations should maintain an active role in disseminating cybersecurity information quickly and concisely through their GSM channels. Specifically, government-operated social media platforms play a significant role in enhancing recent governmental endeavors focused on advancing cybersecurity. Through these platforms, governments can swiftly disseminate crucial information regarding emerging cyber threats, best practices for online safety and updates on cybersecurity policies and regulations. Similarly, governments may effectively use the extensive reach and convenient accessibility of social media platforms to interact directly with citizens, thereby cultivating a collective feeling of accountability and empowerment in the protection of digital assets. Furthermore, social media platforms play a crucial role in facilitating instantaneous communication, allowing governments to rapidly disseminate alerts and updates. This, in turn, aids individuals in being watchful against the ever-changing landscape of cyber dangers. Moreover, these platforms offer opportunities for interactive communication, enabling individuals to seek advice, exchange knowledge and engage in cooperative endeavors aimed at enhancing cybersecurity resilience. GSM serves to both expand the scope of cybersecurity awareness programs and cultivate a more knowledgeable and involved populace, which is essential for improving the overall cybersecurity posture.
5.3 Conclusions
This study uses a quantitative survey and PLS–SEM to examines the influence of GSM and organizational policy compliance on behavioral aspects of cybersecurity. Additionally, this study extends the PMT and cultivation theory by introducing employee protective behavior as a dependent variable and constructing a conceptual framework that integrates cultivation effects with GSM. The results offer novel insights into the complex interplay among GSM, cybersecurity awareness, information protection motivation and employee protective behavior. Specifically, cybersecurity awareness positively impacts both information protection motivation and employee protective behavior. Moreover, GSM positively affects cybersecurity awareness and information protection motivation, with cybersecurity playing a partial mediating role in the relationship between GSM and information protection motivation. Furthermore, a significant positive correlation exists between information protection motivation and employee protective behavior, and information protection motivation partially mediates the relationship between cybersecurity awareness and employee protective behavior. Finally, organizational policy compliance significantly enhances cybersecurity awareness. However, organizational policy compliance does not directly impact employee protective behavior; instead, this relationship is fully mediated by cybersecurity awareness.
5.4 Limitations and future studies
While this study provides new insights into theory and practice, it has certain limitations. First, measuring employee protective behavior using a self-report quantitative questionnaire may lack validity. Self-reports may not be reliable predictors of employees' actual behavior, as their perceptions of security behavior might not align with their real security practices. Longitudinal research would enable more accurate records of actual behavior records but require more time and effort. Second, control variables such as gender, job title and organizational size are not considered, and it would be valuable to explore how these factors influence the established relationships. Third, investigating additional variables at the individual, organizational and social levels would provide a more comprehensive view of the antecedents of employees’ protective behaviors.
Funding: This research is funded by International University, VNUHCMC, Vietnam; SV2022-P M-03.